We live in incredible times with such possibilities that is clear. Although its easily dismissed seeing more centralised downtime, seeing a surge of ransomware and hearing about Voice as a vector for attack.
To quote Buckminster Fuller “You never change things by fighting the existing reality. To change something, build a new model that makes the existing model obsolete.”
You are seeing aspects of this with reading about the path aware networking proposal (Scalability, Control, and Isolation On Next-Generation Networks), Google providing an element of transparency and artificial intelligence used to restore the missing parts of a Rembrandt.
Digital Infrastructure as the core of the European internet
Ian thinks: There is so much good thinking here from Nesta’s Katja Bego. This why the infrastructure is so important as a base for privacy focused better/smarter systems.
Labelling retouched photos
Ian thinks: This is great news and hope it spreads to other EU nations and further a field. Although it should also cover video and audio and highlight whats in the metadata too.
You have YouTube regrets? Join the massive line
Ian thinks: So many of been horrified by where Youtube recommendations can lead you, and this crowdfunded campaign speaks volumes. Will Google do anything about this, its very unlikely.
Our digital legacy in data
Ian thinks: Elaine is right on the button, if you think the data ecosystem is bad now, what happens when most of the dead outnumber the living on social networks. Those terms and conditions need a massive reform.
Steve Wozniak on the right to repair
Ian thinks: Although its a cameo video and its Wozniak, I do think his thoughts are genuine. Does this make much of a difference in the right to repair? Unlikely.
Have you noticed the price increase of Uber?
Ian thinks: I wonder how much of this is the drivers, public understanding of the gig economy and the investors finally wanting their return on investment?
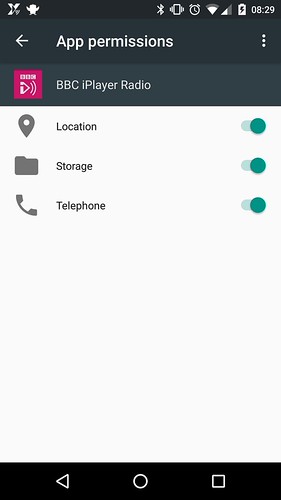
Those apps are selling your most private data
Ian thinks: Its funny but with a deadly serious message. Its also well researched too, its good to see the data ownership/misuse is getting attention everywhere. Even the daily show.
Its time to make the decentralised systems more common and friendly
Ian thinks: Although I don’t agree with everything said here, there is a need to change things and for me it comes down to user experience.
A new future for Solar power
Ian thinks: Great to see the advancement in the use of solar power technology. Using rocks personally surprised me but makes a lot of sense.
Find the archive here