Its been all over the news recently.
Apple’s stunning ‘Liquid Glass’ design could change everything and Andorid’s material 3 design change.
These user interface changes I have lots of thoughts about them from a design and UI point of view (most which has been said elsewhere). However my biggest thought is the underlying problems of our smartphones and our tired notions. (especially since finishing the book The Anxious Generation by Jonathan Haidt and the The Chaos Machine by Max Fisher.
It strikes me, these are the horrible phase of a pig with a touch of lipstick.
The whole way we use smartphones is broken, I’m not that excited about glassy or blobby elements but it feels like were not getting to the root of the issue. Abuse of user/owner data, lack of user/owner agency and the mass surveillance of millions of people through their smartphones can’t got on as its has…
I’d love to see a new paradigm in the same way both companies have tried to tackle the huge rise in smartphone thief’s. Its not like we don’t have the technology to provide advanced protections for user data but rather each one (Apple & Google) benefit from access to the data. I know people will say yes Google but Apple protects user data access? Likely they do but then become the gatekeeper to your data means they can also offer it to trusted parties?
However this isn’t about that question, I’m questioning why so much work has gone into the UI and not into how to make reconsidering the problems of how we use them?

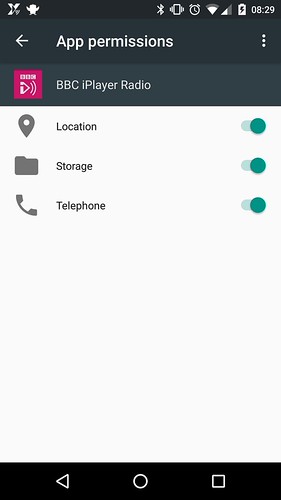
Using the scoped storage as a example. This limits an application to a certain space on the file system. iOS and now Android support this, but its a little clunky and almost encourages the owner of the phone to just accept all (This old tread highlights the problem).
Android recently put more emphasis on modes (basically profiles, which have been tried over and over again). It wouldn’t be difficult to tie modes to permissions too? The difference could be the user interface? I don’t have solid answers but I think about when (rarely) my Pixel goes into power saving mode when the battery is less than 20%. There is a visual UI clue but also it restricts the background data use too. I have heard about people turning on extreme power saving mode always for many reasons.
Some of you might say so what? This isn’t permissions and data but ultimately its the combination which is important. Its almost like their aim is just shift more new phones, regardless of the result… Of course! Some of you may say hey Ian, what would you change and how? My answer is simply I could rethink a bunch of things and I’m sure some of their teams already have but as usual its so low on the list as it doesn’t sell phones. Or even maybe they are waiting for regulation to force them to make the change?

I reflect on the AI/Gemini changes in Android and Google services, maybe I would like to use it for a limited scope of things and accept the results won’t be as great. But my only option is accept or decline. In 2025 this is bad and needs changing, heck I love for designers to take up the challenge of making this all seamlessly work with the ability to negotiate and change the scope at any time.
Really need to see Human Data Interaction replace Human Computer Interaction now because its become unacceptable in my eyes. Worst still it limits whats possible and leads to a outcome which doesn’t empower the owner/users.